New Relic Should Detect a Disrupted Workflow when a Workload Is Unavailable
New Relic Should Detect a Disrupted Workflow when a Workload Is Unavailable
New Relic Should Detect a Disrupted Workflow when a Workload Is Unavailable
New Relic Should Detect a Disrupted Workflow when a Workload Is Unavailable
Verify that New Relic alerts you to disruptions in your workflow, such as a critical deployment without pods ready to serve traffic.
Motivation
Kubernetes features a liveness probe to determine whether your pod is healthy and can accept traffic. If Kubernetes cannot probe a pod, it restarts it in the hope that it will eventually be ready. In case it is a critical deployment, New Relic workflow should alert on this disruption
Structure
First, check that the New Relic Workflow is marked as operational As soon as all pods of a workload aren't reachable, caused by the block traffic attack, New Relic should detect this by marking the workflow as disrupted and ensuring your on-call team is taking action.
Solution Sketch
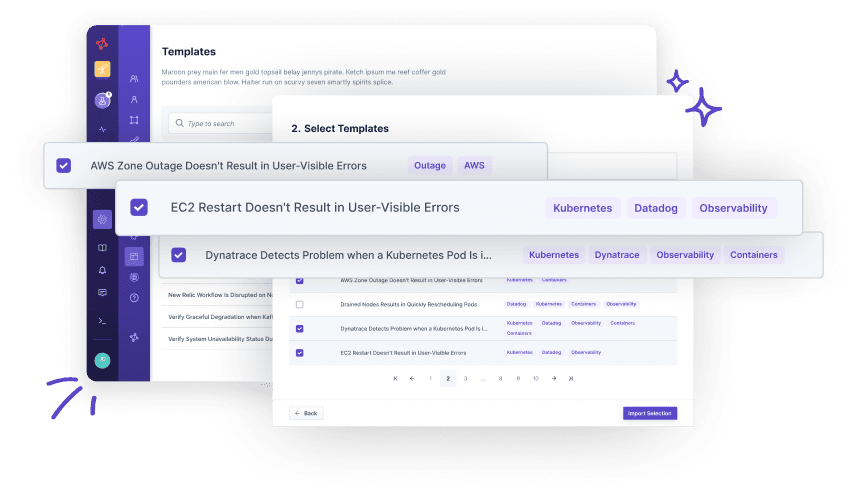
How to use this template?
Import via Hub Connection
Steadybit’s Reliability Hub is already connected to your platform. If you are an admin, you can just easily import templates with just one click.
Are you on-prem?
This is how you import Templates